If you want to guarantee your privacy, follow these steps:
- If you use Facebook, YouTube, Facebook Messenger, Instagram, Tumblr, Twitter, Skype, Google+, Snapchat, Reddit, LinkedIn, Pinterest, WhatsApp,
 Quora, or any other Social Media, cancel your account. Some of these companies may been lax about security in the past. Most are doing the best they can to protect us, but … nothing on the Internet is completely secure all the time. How can we expect privacy when we put so much personal information on these sites?
Quora, or any other Social Media, cancel your account. Some of these companies may been lax about security in the past. Most are doing the best they can to protect us, but … nothing on the Internet is completely secure all the time. How can we expect privacy when we put so much personal information on these sites?
- If you have an Amazon Echo, a Google Assistant, an Apple Homepod, Invoke, or any other Smart Speaker, disconnect and destroy it.
 In order to be our obedient little servants, Smart Speakers listen to everything we say. They are activated when they hear their “names” (Alexa, Siri, OK Google, etc.). Most of them record our queries in order to build context … to “understand” us and our needs. Are queries the only thing they record? Do we know they aren’t recording every word?
In order to be our obedient little servants, Smart Speakers listen to everything we say. They are activated when they hear their “names” (Alexa, Siri, OK Google, etc.). Most of them record our queries in order to build context … to “understand” us and our needs. Are queries the only thing they record? Do we know they aren’t recording every word?
- If you have any Internet-capable Devices, disable their Internet access or stop using them. Commonly called the “Internet of Things“,
 Internet-capable Devices include everything from lights that can be controlled remotely to refrigerators that let you see what’s inside while you’re in the grocery store. In order to accomplish these “miracles”, these devices must connect to the Internet … and the Internet can connect to them. In October of 2016, hackers used the Internet of Things as a path into a company whose servers support a number of popular websites. The attack disrupted Internet services for most of a day.
Internet-capable Devices include everything from lights that can be controlled remotely to refrigerators that let you see what’s inside while you’re in the grocery store. In order to accomplish these “miracles”, these devices must connect to the Internet … and the Internet can connect to them. In October of 2016, hackers used the Internet of Things as a path into a company whose servers support a number of popular websites. The attack disrupted Internet services for most of a day.
- If you have a mobile phone, smash it and cancel your cellular service. If you have an old style cell phone,
 you’re a little safer than if you have if you have a “smartphone“. Both have computers inside. The computers in an old style cell phone “know” how to handle voice and … probably … text messages. The computers in a smartphone “know” how to handle anything a tablet, laptop, or even a desktop can. A smartphone is a handheld Internet engine … subject to the same security concerns. When connected through the cellular network, the smartphone is a bit more secure than a tablet or laptop. When connected through WIFI, smartphone security is exactly the same the tablet or laptop. Even on the cellular network, your voice and text is travelling through the air initially. Cellular may be harder to capture and decrypt, but it’s not impossible.
you’re a little safer than if you have if you have a “smartphone“. Both have computers inside. The computers in an old style cell phone “know” how to handle voice and … probably … text messages. The computers in a smartphone “know” how to handle anything a tablet, laptop, or even a desktop can. A smartphone is a handheld Internet engine … subject to the same security concerns. When connected through the cellular network, the smartphone is a bit more secure than a tablet or laptop. When connected through WIFI, smartphone security is exactly the same the tablet or laptop. Even on the cellular network, your voice and text is travelling through the air initially. Cellular may be harder to capture and decrypt, but it’s not impossible.
- If you are reading this article on-line, finish reading it (if you dare), then stop using the Internet. Internet Security is an oxymoron.
 Between malicious software (viruses, trojan horses, worms, spyware, etc.), “denial of service” attacks, phishing, and applications vulnerable to hacking, the Internet is “out to get you”. Internet Service Providers (ISPs), application and operating system developers, website hosting services, and website developers are in an unending war against hackers, criminals, and industrial or intergovernmental spys/attackers.
Between malicious software (viruses, trojan horses, worms, spyware, etc.), “denial of service” attacks, phishing, and applications vulnerable to hacking, the Internet is “out to get you”. Internet Service Providers (ISPs), application and operating system developers, website hosting services, and website developers are in an unending war against hackers, criminals, and industrial or intergovernmental spys/attackers.
- If you use Google, Bing, Yahoo!, or other Search Engines, stop. Search Engines provide links to websites and data repositories.
 Even The Shadow doesn’t know what evils lurk in the hearts of Internet sites. The easiest way to avoid dangerous places on the internet is to stop looking for “places” to go. To make matters worse, many websites capture information from your computer or smartphone … and those devices can even know where you are. Big Brother can easily be watching you.
Even The Shadow doesn’t know what evils lurk in the hearts of Internet sites. The easiest way to avoid dangerous places on the internet is to stop looking for “places” to go. To make matters worse, many websites capture information from your computer or smartphone … and those devices can even know where you are. Big Brother can easily be watching you.
- If you store any data on “The Cloud“, copy it to local storage, then delete it. Although Cloud Computing is somewhat secure,
 businesses and individual users have treated it as if it were a vault with multiple locks and surrounded with armed guards 24 hours a day. High profile data breaches in the news have painted a different picture. No data storage system is inherently secure. Its designers must build security into the system and applications that interact with the system. At the same time, users of the system must remain responsible for their own data. Unencrypted passwords, keys, etc. are not acceptable. Even that multi-locked and guarded vault can be breached.
businesses and individual users have treated it as if it were a vault with multiple locks and surrounded with armed guards 24 hours a day. High profile data breaches in the news have painted a different picture. No data storage system is inherently secure. Its designers must build security into the system and applications that interact with the system. At the same time, users of the system must remain responsible for their own data. Unencrypted passwords, keys, etc. are not acceptable. Even that multi-locked and guarded vault can be breached.
- If you use e-mail, stop. This is almost a no-brainer.
 Most e-mail is unencrypted. Some e-mail interfaces are less than secure. Who knows whether the e-mail servers are secure. Does this sound like a good way to share information and retain privacy?
Most e-mail is unencrypted. Some e-mail interfaces are less than secure. Who knows whether the e-mail servers are secure. Does this sound like a good way to share information and retain privacy?
- Delete Microsoft Edge, Google Chrome, Mozilla Firefox, any other Internet Browser, and any Mail Client from your computer.
 You’ve already stopped using Search Engines and e-mail. What other need do you have for an application that has viewing websites as its sole purpose? On-line shopping … where you cheerfully hand out your name, address, purchasing preferences, and your credit card information? Doesn’t sound too smart.
You’ve already stopped using Search Engines and e-mail. What other need do you have for an application that has viewing websites as its sole purpose? On-line shopping … where you cheerfully hand out your name, address, purchasing preferences, and your credit card information? Doesn’t sound too smart.
- If your computer uses WiFi, disable it. If you can get out of your computer using wireless networking, they can get in.
 (They equals hackers, criminals, governments, etc.). WiFi software on your computer was designed to create connections that you initiate, but who knows what hidden applications you may have picked up from earlier insecure use of Social Media, Search Engines, The Cloud, e-mail, etc.? WiFi Services are everywhere!
(They equals hackers, criminals, governments, etc.). WiFi software on your computer was designed to create connections that you initiate, but who knows what hidden applications you may have picked up from earlier insecure use of Social Media, Search Engines, The Cloud, e-mail, etc.? WiFi Services are everywhere!
- If your computer is connected to the Internet, disconnect it. As with WiFi, really skilled digital intruders
 can sneak in malicious software that allows them to reverse connect through a cable connection. Besides, your only remaining reason to be connected to the Internet would be to break into someone else’s computer.
can sneak in malicious software that allows them to reverse connect through a cable connection. Besides, your only remaining reason to be connected to the Internet would be to break into someone else’s computer.
- Stop using Credit Cards and Debit Cards. Yes, they’re convenient. (Probably too convenient … they make it easy to get deeply into debt.) Yes, they’re more secure than they used to be.
 But, do you remember how much information you provided to get those things? Your name, address, phone number, e-mail address, and access to your credit rating are dangerous enough, but every time you use one of these cards, you let the issuer know where you are and a general idea of what you’re buying. Over time, they can develop a good profile of your behavior.
But, do you remember how much information you provided to get those things? Your name, address, phone number, e-mail address, and access to your credit rating are dangerous enough, but every time you use one of these cards, you let the issuer know where you are and a general idea of what you’re buying. Over time, they can develop a good profile of your behavior.
- If you have an Internet Service Provider (ISP), cancel the service. Your ISP connects you to systems all over the world.
 It gives you a window to the whole world. Oh wait, you just disabled your WiFi and removed your network cable. You’re paying big bucks for something you’re not using. D’oh! Keep your subscription money. If you don’t know what to do with the savings, give it to charity.
It gives you a window to the whole world. Oh wait, you just disabled your WiFi and removed your network cable. You’re paying big bucks for something you’re not using. D’oh! Keep your subscription money. If you don’t know what to do with the savings, give it to charity.
- Shut down your Computer, unplug it, and remove any batteries. Yes, if you have the right software, you can still use your computer
 to keep records, play games against the machine or your own high score, you can write prose or poetry, you can draw, you can print what you write or draw (but only if you have an attached printer) … or, you can get some paper, pencils, and a deck of cards for solitaire, then stop wasting electricity.
to keep records, play games against the machine or your own high score, you can write prose or poetry, you can draw, you can print what you write or draw (but only if you have an attached printer) … or, you can get some paper, pencils, and a deck of cards for solitaire, then stop wasting electricity.
- Remain alert and watchful. This seems obvious, but bears mentioning because of the heightened risk.
 Attacks on privacy are everywhere … from Closed Circuit TVs (CCTV) watching every street corner to “Security Theater” at airports, sporting events, etc. We’re told these devices and procedures are designed to uphold the law and keep us safe. Laws can be abused; to be completely safe, one must be completely controlled.
Attacks on privacy are everywhere … from Closed Circuit TVs (CCTV) watching every street corner to “Security Theater” at airports, sporting events, etc. We’re told these devices and procedures are designed to uphold the law and keep us safe. Laws can be abused; to be completely safe, one must be completely controlled.
- If you have a landline, cancel your service and remove the phone(s). Our government is required to get a warrant in order to listen in on our calls, but do they always do so?
 Do you believe that the government is always following the law … and always will? Who else might be listening to your calls? Criminals don’t need warrants. Are you sure your phone can’t be used to monitor you all of the time. It has a microphone and electronic components.
Do you believe that the government is always following the law … and always will? Who else might be listening to your calls? Criminals don’t need warrants. Are you sure your phone can’t be used to monitor you all of the time. It has a microphone and electronic components.
- Unplug all TVs and Radios. TVs and Radios have speakers. What’s the difference between a speaker and a microphone?
 Not much. The speaker transforms an electrical impulse into a mechanical vibration. A microphone transforms a mechanical vibration into an electrical impulse. Other than size, it’s the electronics behind each that makes the difference. If you can hear your TV or Radio, it could have the bidirectional electronics to let it listen to you.
Not much. The speaker transforms an electrical impulse into a mechanical vibration. A microphone transforms a mechanical vibration into an electrical impulse. Other than size, it’s the electronics behind each that makes the difference. If you can hear your TV or Radio, it could have the bidirectional electronics to let it listen to you.
- Don’t let Authority Figures intimidate you. Authority Figures are not always right. In fact, the longer any person or small, closed group remains in authority; the more likely that person or group will give in to the lure of Despotism.
 These individuals may try to give the impression that they are guided by the Will of the People … they may even delude themselves into believing their own lies, but the tendency toward accumulating power is strong. The less we question; the more likely we are to suffer from “hardening of the categories”. Don’t be intimidated. Question everything that bothers you. Stand your ground no matter how insignificant you feel. Maybe … just maybe … you aren’t alone. If you screw up, don’t give a crap, BUT … use your error to adjust your perspective and grow.
These individuals may try to give the impression that they are guided by the Will of the People … they may even delude themselves into believing their own lies, but the tendency toward accumulating power is strong. The less we question; the more likely we are to suffer from “hardening of the categories”. Don’t be intimidated. Question everything that bothers you. Stand your ground no matter how insignificant you feel. Maybe … just maybe … you aren’t alone. If you screw up, don’t give a crap, BUT … use your error to adjust your perspective and grow.
- If you use “snail mail”, stop. Do you want the Government to know where you are? The full name of the organization carrying your mail is The United States Postal Service (USPS), you know.
 Do you trust your postal carrier? He or she is an agent of the Federal Government. (Don’t let that phrase “independent agency of the United States federal government” confuse you. That’s probably what they want.) Are you sure your carrier isn’t spying on you? Are you sure the USPS doesn’t keep a record of everybody’s mail? Better to avoid “snail mail” altogether.
Do you trust your postal carrier? He or she is an agent of the Federal Government. (Don’t let that phrase “independent agency of the United States federal government” confuse you. That’s probably what they want.) Are you sure your carrier isn’t spying on you? Are you sure the USPS doesn’t keep a record of everybody’s mail? Better to avoid “snail mail” altogether.
- Replace all Electric Clocks with Wind-up Clocks. Have you ever looked inside a clock? The picture on the left shows the internals of a mechanical clock.
 It looks complicated, but the parts are recognizable … gears, levers, springs, etc. The picture on the right shows the internals of an electronic clock. It looks simple, but do you recognize the parts? There seems to be one gear near the center and the battery is at the top, but what’s all that other stuff? Who knows whether or not any of them compromise your privacy.
It looks complicated, but the parts are recognizable … gears, levers, springs, etc. The picture on the right shows the internals of an electronic clock. It looks simple, but do you recognize the parts? There seems to be one gear near the center and the battery is at the top, but what’s all that other stuff? Who knows whether or not any of them compromise your privacy.
- Stay away from crowds. Part of your quest for privacy may be related to avoiding others
 who may make judgements about your behavior and interfere with your life. News reports are filled with cases of someone making a poor judgement or seeking revenge, calling 911 with incorrect information or outright lies. The police, who must take such calls seriously, enter the situation expecting trouble and another tragedy occurs. If you stay away from people … especially crowds … that can’t happen. Besides, for all you know, there may be telepaths in those crowds. Protecting your privacy from them takes a lot of “tin foil“.
who may make judgements about your behavior and interfere with your life. News reports are filled with cases of someone making a poor judgement or seeking revenge, calling 911 with incorrect information or outright lies. The police, who must take such calls seriously, enter the situation expecting trouble and another tragedy occurs. If you stay away from people … especially crowds … that can’t happen. Besides, for all you know, there may be telepaths in those crowds. Protecting your privacy from them takes a lot of “tin foil“.
- Don’t drive any car built after 1956. Most of us are aware that modern automobiles are filled with electronic sensors
 and servo-mechanisms controlled by one or more computers. You may have heard news reports about hackers taking control of modern cars. Unless you’re an antique car aficionado, you probably didn’t know that electronics … in the form of an electronic fuel injection system … began to creep into our vehicles as early as 1957. A working car built in 1956 or earlier may be hard to find; it will lack every safety feature introduced into motor vehicles over the past 60+ years; BUT … you’ll be able to drive it without worrying that someone will take control and drive you into a ditch.
and servo-mechanisms controlled by one or more computers. You may have heard news reports about hackers taking control of modern cars. Unless you’re an antique car aficionado, you probably didn’t know that electronics … in the form of an electronic fuel injection system … began to creep into our vehicles as early as 1957. A working car built in 1956 or earlier may be hard to find; it will lack every safety feature introduced into motor vehicles over the past 60+ years; BUT … you’ll be able to drive it without worrying that someone will take control and drive you into a ditch.
- Mind your own business. If you want to have your privacy respected,
 you must respect the privacy of others. Doing otherwise would be hypocritical and opens the door for others to mind your business. You’ve already disposed of the electronic sources of misinformation. Stay away from the built-in sources … the gossip you hear and what you think you see.
you must respect the privacy of others. Doing otherwise would be hypocritical and opens the door for others to mind your business. You’ve already disposed of the electronic sources of misinformation. Stay away from the built-in sources … the gossip you hear and what you think you see.
- Be prepared to protect yourself. Not like the kitten in the picture … he’s part of an entirely different potential invasion.
 Day-to-day invasions of your privacy are subtle. Many “big box” stores have enticements to encourage you to shop there. To be eligible for those enticements, you need to sign-up. The cashier may ask if you want to join the program. If you agree, the store needs a record of you. You no longer have a phone number nor an e-mail address, but you still have a street address. Don’t provide it. Better yet, reject the sign-up offer.
Day-to-day invasions of your privacy are subtle. Many “big box” stores have enticements to encourage you to shop there. To be eligible for those enticements, you need to sign-up. The cashier may ask if you want to join the program. If you agree, the store needs a record of you. You no longer have a phone number nor an e-mail address, but you still have a street address. Don’t provide it. Better yet, reject the sign-up offer.
- Move to a remote cabin outside Lincoln, Montana. You may be able
 to eliminate a street address by going to a small town, in a large state with a small population, buying a small plot of land, and building a small, ultra-low tech (no indoor plumbing) shack to call home. It worked for Ted Kaczynski … for a while at least.
to eliminate a street address by going to a small town, in a large state with a small population, buying a small plot of land, and building a small, ultra-low tech (no indoor plumbing) shack to call home. It worked for Ted Kaczynski … for a while at least.
- Try to avoid mailing manifestos and bombs. Congratulations! Other than a trip into town for supplies every week or two,
 you never need to see or interact with anybody. The more you can grow and build; the less often you need to deal with anyone. You have your privacy … and you’ve become a perfect example of a Luddite. The rest of the world may trade some privacy for convenience and society … but, that’s none of your business.
you never need to see or interact with anybody. The more you can grow and build; the less often you need to deal with anyone. You have your privacy … and you’ve become a perfect example of a Luddite. The rest of the world may trade some privacy for convenience and society … but, that’s none of your business.
Is there no way to protect my privacy without “moving” to the Middle Ages?
No, not really; not complete privacy. Participation in our modern world and protecting one’s privacy is a trade-off.  We have been giving up some of our privacy to gain society almost since we climbed out of the trees (if, in fact, “the trees” were our origin). Speech … and the communications pantomime that preceded it … was one of the first examples of giving up some privacy. Before we communicated with others, our thoughts were our own. If we avoided others, our behavior was too. Communication was the beginning of the Privacy Paradox … our willingness to trade privacy for society.
We have been giving up some of our privacy to gain society almost since we climbed out of the trees (if, in fact, “the trees” were our origin). Speech … and the communications pantomime that preceded it … was one of the first examples of giving up some privacy. Before we communicated with others, our thoughts were our own. If we avoided others, our behavior was too. Communication was the beginning of the Privacy Paradox … our willingness to trade privacy for society.
Writing was next. When we invented the written word, we gave technology a means for invading our privacy.  Now, we were sharing our thoughts … tiny pieces of our innermost being … with not only our immediate companions, but also with anyone who could decipher the marks on a clay tablet, parchment, or piece of paper … including those yet unborn. Where would it end?
Now, we were sharing our thoughts … tiny pieces of our innermost being … with not only our immediate companions, but also with anyone who could decipher the marks on a clay tablet, parchment, or piece of paper … including those yet unborn. Where would it end?
Technology began to attack our privacy in the early 16th Century when Magellan‘s ships used cannons and flags to communicate at a distance. In the late 18th Century, Claude Chappe developed long-distance communications using a series of semaphore relay stations. In the early 19th Century, Joseph Henry developed an electric telegraph and was quickly followed by Samuel Morse inventing his code that made it possible to quickly transmit messages across continents and later oceans.  The invention of the Telephone near the end of the 19th Century dealt a blow to our privacy from which we have never recovered. Did the phone line have an odd background buzz because someone was listening in on the party line … or was it just the wind or a bunch of birds resting on a wire somewhere? Did the operator back out after connecting our call … or was she “listening in”. Can we ever be safe again?
The invention of the Telephone near the end of the 19th Century dealt a blow to our privacy from which we have never recovered. Did the phone line have an odd background buzz because someone was listening in on the party line … or was it just the wind or a bunch of birds resting on a wire somewhere? Did the operator back out after connecting our call … or was she “listening in”. Can we ever be safe again?
Yes, even in a computer-filled Internet age, we can be relatively safe … not as safe as if we were living in isolation in a shack … or a cave … or a tree …, but most of us don’t want that.
Some sensible steps for protecting our privacy in the 21st Century:
- Secure your computers, smartphones, and Routers:
- Be sure your software and firmware is up to date. The companies who sell these products want to keep you coming back.
 Most of them want to protect you from malicious “outsiders”. They regularly provide updates that enhance both security and performance. There is no additional cost for these updates. When they’re provided, install them. It’s worth the time needed to do so.
Most of them want to protect you from malicious “outsiders”. They regularly provide updates that enhance both security and performance. There is no additional cost for these updates. When they’re provided, install them. It’s worth the time needed to do so.
- Purchase and install anti-virus software. There are a number of quality products for computers
 and smartphones. Some of the products work on both. If you don’t want to purchase another product, activate all of the network security built into your system’s operating system … especially the Firewall.
and smartphones. Some of the products work on both. If you don’t want to purchase another product, activate all of the network security built into your system’s operating system … especially the Firewall.
- Don’t download or install any software without a little research. Look for reviews of the application. Make sure it’s not sneaking malicious code into your device.
- Be sure your software and firmware is up to date. The companies who sell these products want to keep you coming back.
- Be aware of Internet and E-mail Addresses.
- Let’s look at Internet addresses first. Before you open a link (URL), take a look at the actual address. In most cases, hovering the cursor over the link will display the actual address … either in the lower left corner of your screen (like this site does) … or, in a pop-up window like this:
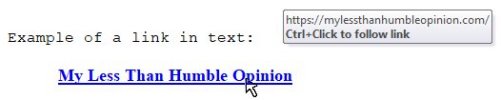
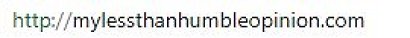
If the actual address appears legitimate, it probably is:

A bogus address will usually look as if someone threw a bunch of letters down a staircase, then picked up the ones that reached the bottom:

The next thing to notice is whether or not the address points to a “secure” site. When you are using a secure site, any information that you send to the site and any information sent to you is encrypted. You and the website have the authentication key … making decryption easy. Any intruder who might intercept the communication gets indecipherable garbage. Secure sites begin with https://

Insecure sites begin with http:// (without the “s”)
- The way to spot questionable e-mail addresses is similar to spotting questionable link addresses … with a slight twist. Businesses and Government Agencies have relatively meaningful addresses like these:
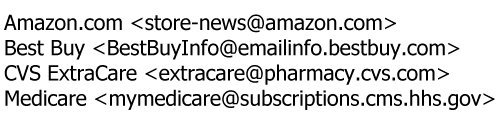
You can see that the actual address inside the angle brackets has some fairly obviously similarities to the display name (e.g., bestbuy in the Best Buy address; mymedicare in the Medicare address). These companies and agencies probably have purchased their own domain names and set up their own mail servers.
If the display names used by “spammers” aren’t enough to make you suspicious. The actual addresses are dead giveaways:

Individuals using public or ISP-based e-mail services have some control over their e-mail addresses. Some create names that are humorous or have a special, personal meaning. Sometimes neither the display name nor the actual address helps you to determine whether the e-mail is “safe”.

Worse yet, spammers and more malicious mailers can pretend to be someone you know. Consider this mail header:
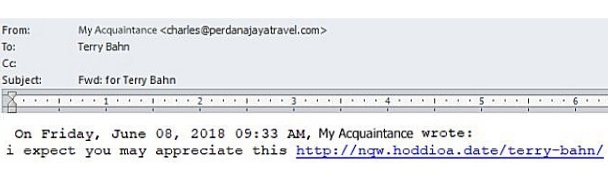 At first, you may see the display name “My Acquaintance” … the name of someone you know. You see your acquaintance’s name again in the text. Even though the text seems a bit odd, you may blithely click on the link in the message … and, you could be in big trouble. Take a closer look at the actual address:
At first, you may see the display name “My Acquaintance” … the name of someone you know. You see your acquaintance’s name again in the text. Even though the text seems a bit odd, you may blithely click on the link in the message … and, you could be in big trouble. Take a closer look at the actual address:
 That’s nowhere close to the correct address is it? Be sure to look closely. If the spammer/malicious mailer knows your acquaintance’s real address (or that of a company from whom you receive mail), a misspelling of the actual address can fool you as well.
That’s nowhere close to the correct address is it? Be sure to look closely. If the spammer/malicious mailer knows your acquaintance’s real address (or that of a company from whom you receive mail), a misspelling of the actual address can fool you as well.
 Note: This is a common trick with URLs too. This is not Facebook …
Note: This is a common trick with URLs too. This is not Facebook …
 … nor is it a secure site. You wouldn’t want to enter any personal information on this site. Be observant. Don’t even go to the site.
… nor is it a secure site. You wouldn’t want to enter any personal information on this site. Be observant. Don’t even go to the site.
- Let’s look at Internet addresses first. Before you open a link (URL), take a look at the actual address. In most cases, hovering the cursor over the link will display the actual address … either in the lower left corner of your screen (like this site does) … or, in a pop-up window like this:
- If you don’t want your information to be public, don’t put it on Social Media.
Anything that you post on Social Media that’s even remotely interesting to anybody (i.e., everything) will live on the Internet (or whatever eventually supersedes it) until the Sun grows old, expands, and consumes the inner planets.
Does the above sentence sound melodramatic and exaggerated? Consider this. The population of the Earth is greater than 7.6 Billion and growing by more than 200,000 persons per day. About 51% … 3.876 Billion … use the Internet. More than 77% of those Internet users … about 3 Billion … have at least one Social Media account. (The average per Internet user is 7.6.) There are 86,400 seconds in a day. On the average, more than 34,700 people with Social Media accounts are on the Internet at any given second. Of course, they’re not all using their Social Media accounts whenever they’re on-line. If only 10% are using their Social Media accounts, that’s 3,470 people. (10% is probably a conservative estimate.)
About 51% … 3.876 Billion … use the Internet. More than 77% of those Internet users … about 3 Billion … have at least one Social Media account. (The average per Internet user is 7.6.) There are 86,400 seconds in a day. On the average, more than 34,700 people with Social Media accounts are on the Internet at any given second. Of course, they’re not all using their Social Media accounts whenever they’re on-line. If only 10% are using their Social Media accounts, that’s 3,470 people. (10% is probably a conservative estimate.)
Now, suppose you post something on (one of) your Social Media site(s); almost immediately, you decide it’s a bit too private to share; and you delete it. Let’s say you reconsider and delete the entry within a minute. If only one one-hundredths of one percent (0.01%) of all Social Media users might have seen your entry during its brief life on the Internet, any one of 20-21 persons might have a record of your entry … and who knows how long an entry sits hidden of a site’s server before it’s really deleted. If the entry reached “The Cloud” it could take time for the deletion request to catch up.
Let’s say you reconsider and delete the entry within a minute. If only one one-hundredths of one percent (0.01%) of all Social Media users might have seen your entry during its brief life on the Internet, any one of 20-21 persons might have a record of your entry … and who knows how long an entry sits hidden of a site’s server before it’s really deleted. If the entry reached “The Cloud” it could take time for the deletion request to catch up.
Be careful with e-mail and Text Messages too. Getting rid of them requires action from at least two people … your recipient and you. If they’re sent to a distribution list or forwarded, they can live forever. If you have a good enough memory, you’ll notice that some “joke messages” make the rounds every 3 to 5 years. There are even some “urban legend” e-mails carrying stories that predate the Internet by many decades.
The Time Machine
Many people long for “The Good Old Days” when life was “better”. Often, if you ask someone what time period they’re talking about, they mention a time when they were children. Well, duh! When all your needs … including privacy … are handled by someone else, life is a lot easier. In case you haven’t guessed, this article’s 26 item list is a virtual time machine. As you progress through the list, you move … by fits and starts … farther backwards in time.
- If you eliminate all Smart Speakers (Amazon Echo, Google Assistant, etc.), you move back to before June 23, 2015.
- Get rid of “The Cloud” and you predate August, 2006.
- To get to 2001, say good-bye to Facebook, YouTube, Twitter, Skype, LinkedIn, and MySpace.
- After every one of the “Internet of Things” is gone, you’ve left the 21st Century. Party like it’s 1999.
- Dump all smartphones and you’ll be “entertained” by the beginnings of the 1992 Presidential Campaign because you’re in 1991.
- Back up one more year and WiFi disappears.
- By 1988, Browsers, the Web, commercial ISPs, and the public Internet are yet to be.
- Getting rid of your personal computer will land you in 1976. Enjoy the United States Bicentennial Celebration.
- The first e-mail was Personal Notes on the PLATO system at the University of Illinois. Without it, you’re in 1973.
- The next time jump is one we’ve discussed above. We leap back to 1956 to dispose of all electronic controls in our cars.
- A practical television system was demonstrated in 1927. Dispose of TV and Radio … you’re living in 1926. Enjoy yourself now. You’re only 3 years before the beginning of the Great Depression.
- Bye-bye landline telephone; bye-bye 20th Century. Welcome to 1875.
- Time measuring devices have existed for over 3500 years, but the electric clock was patented in 1840. Martin Van Buren is President of the United States.
- Persian King Cyrus the Great is credited with creating a postal system in 550 BC.
- Although Lincoln, Montana didn’t exist until the late 19th Century, humans did begin building houses sometime between 9000 BC and 5000 BC. There’s probably little to protest, manifestos would have to be chiseled in stone … and you’d have to deliver them yourself. With bomb-making difficult if not impossible, maybe you could hit someone with the manifesto stone if you really saw a need for violence.
Congratulations!
Your Privacy is (relatively) secure at last.

